A government facility's CMMS holds far more than maintenance schedules. It contains building blueprints, HVAC access points, security system configurations, and infrastructure vulnerability data that represent exactly the kind of target federal cybersecurity mandates were written to protect. Yet most agencies still run legacy on-premise servers or commercial SaaS tools that fail basic FISMA audits — leaving critical infrastructure data exposed to threats that a compliant, purpose-built platform would eliminate. Whether you manage federal buildings, state facilities, or public infrastructure, your CMMS must meet FedRAMP, FISMA, and NIST SP 800-53 standards — or it is a liability, not an asset. Sign up free to see how OxMaint meets government-grade security requirements from day one, or book a demo to assess your agency's current software security posture.
Government-Grade CMMS Security — FedRAMP Aligned, FISMA Ready
OxMaint brings together asset management, zero-trust architecture, AES-256 encryption, continuous threat monitoring, and automated compliance reporting — purpose-built for public sector facilities that cannot afford a compliance gap.
FISMA vs. FedRAMP: What Your Agency Actually Needs to Understand
These two frameworks are related but not interchangeable, and confusing them is one of the most common compliance mistakes in government IT procurement. FISMA governs what your agency must do to secure its information systems — it is a law that creates the obligation. FedRAMP governs what cloud service providers must prove before your agency can use them — it is the authorization mechanism that fulfills FISMA's cloud-specific requirements. When your agency adopts a cloud-based CMMS, FISMA creates the mandate and FedRAMP is how the vendor satisfies it. Book a demo to review OxMaint's compliance documentation for your agency's procurement team.
- Applies to all federal agencies and their information systems
- Requires agencies to categorize systems as Low, Moderate, or High impact
- Mandates agency-wide security programs, risk assessment, and continuous monitoring
- Also applies to state agencies managing federally funded programs
- Private contractors working with federal agencies must comply
- Focuses exclusively on cloud service providers used by federal agencies
- Requires third-party independent assessment before authorization
- Establishes Low, Moderate, and High security baselines for cloud services
- Once authorized, a CSP can be adopted by any federal agency
- FedRAMP 20x modernization underway — automation-driven compliance from 2025
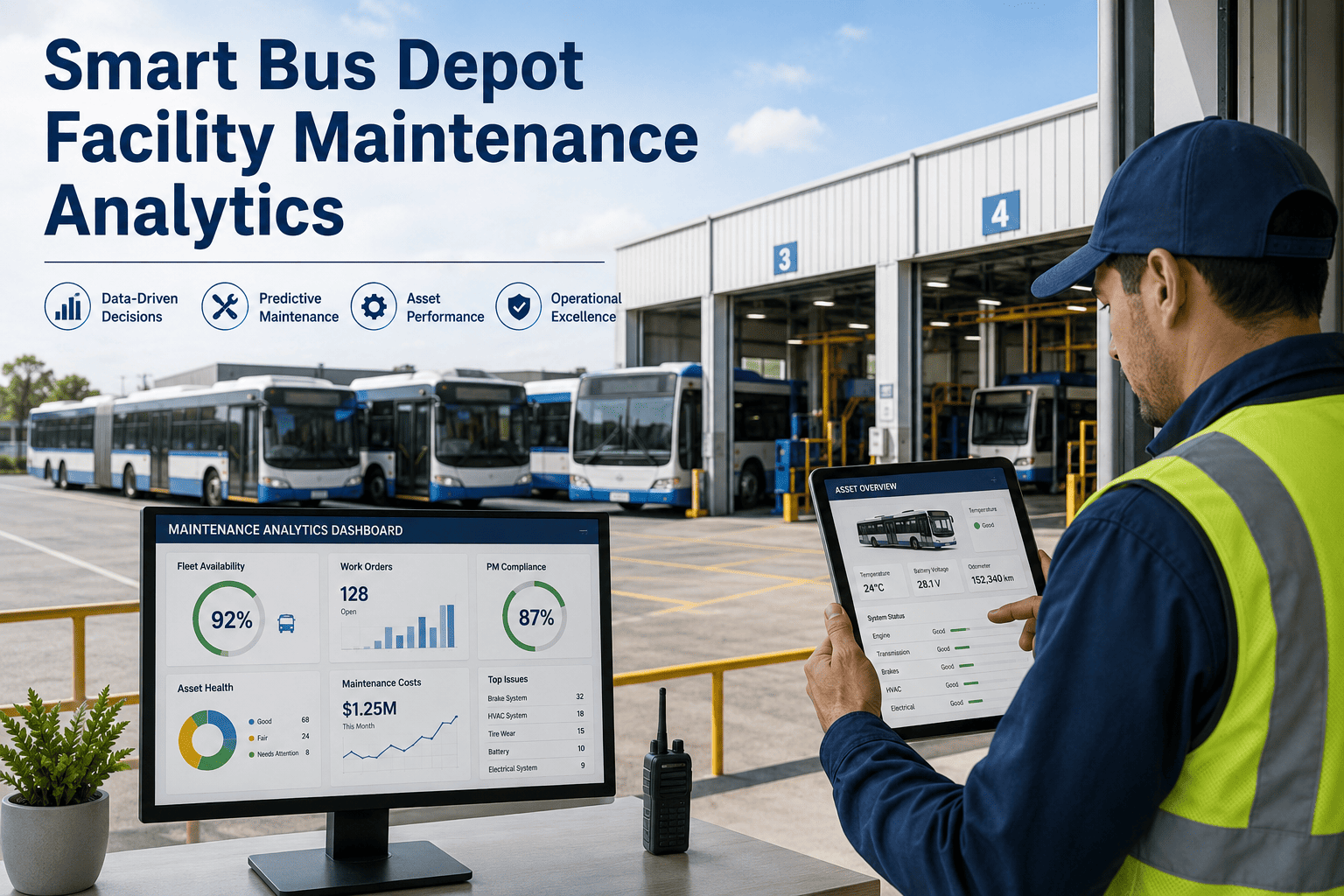
Why CMMS Data Is a High-Value Security Target
Public sector CMMS platforms hold data that goes far beyond maintenance schedules. Building blueprints, access control configurations, fire suppression system layouts, HVAC zones, security camera positions, and critical infrastructure inspection records create a complete operational picture of a facility. In 2023 alone, US federal agencies reported over 32,000 information security incidents. A CMMS with inadequate access controls, unencrypted data at rest, or no audit logging is not just a compliance failure — it is an active vulnerability in your physical security posture. Sign up free to start managing your facilities on a compliant, zero-trust foundation from day one.
Floor plans, mechanical room locations, utility access points — all stored in asset records. Without role-based access controls, any user can export a complete facility schematic.
Work order histories reveal when security systems are offline for maintenance, when HVAC zones are accessible, and which contractors have unescorted access to sensitive areas.
Inspection records documenting deferred maintenance, failing equipment, and known deficiencies are exactly the intelligence a bad actor needs to identify exploitable weaknesses in critical infrastructure.
CMMS platforms without NIST AU-family compliant event logging — recording who accessed what, when, and from where — cannot support FISMA audit requirements or incident reconstruction after a breach.
Required Security Controls: What a Compliant Government CMMS Must Have
NIST SP 800-53 Rev. 5 defines the security and privacy control families that government information systems must implement. For a CMMS at Moderate impact level — the baseline for most civilian agency facility systems — these are the non-negotiable controls your platform must demonstrate. Book a demo to review OxMaint's NIST 800-53 control mapping for your agency's ATO package.
| Control Family | NIST 800-53 Requirement | OxMaint Implementation |
|---|---|---|
| Access Control (AC) | Role-based access, least privilege, session management, remote access controls | RBAC with granular permissions, SAML 2.0 SSO, MFA enforcement, session timeout controls |
| Audit & Accountability (AU) | Event logging, audit log protection, log retention, review and reporting | Tamper-evident audit logs, configurable retention, SIEM export, complete user action trail |
| Configuration Management (CM) | Baseline configuration, change control, security impact analysis | Configuration baselines documented, change approval workflow, security impact review gates |
| Identification & Authentication (IA) | User identification, authentication management, multi-factor authentication | PIV/CAC-compatible authentication, MFA at all access levels, credential lifecycle management |
| System & Communications Protection (SC) | Encryption in transit, network segmentation, boundary protection | TLS 1.3 in transit, AES-256 at rest, isolated tenant environments, zero-trust network access |
| Incident Response (IR) | Incident handling capability, reporting, testing | Documented IR plan, 72-hour breach notification, continuous threat monitoring, annual IR testing |
FedRAMP Impact Levels: Which Applies to Your CMMS
FedRAMP authorization comes in three impact levels that determine the security baseline your CMMS vendor must satisfy. The level is set by your agency's data classification — what information the system processes, stores, or transmits. Getting this wrong in either direction creates risk: under-classified means inadequate controls; over-classified creates unnecessary procurement barriers. Sign up free and discuss your agency's data classification requirements with OxMaint's government compliance team.
Limited adverse effect if data is compromised. Typically applies to publicly available information or non-sensitive operational data. Most civilian facility CMMS instances with no restricted access data.
Serious adverse effect if compromised. Applies to most civilian agency CMMS systems handling PII, building security data, infrastructure layouts, or contractor access records. The baseline for most government facility platforms.
Severe or catastrophic adverse effect. Required for CMMS systems at military installations, classified research facilities, law enforcement infrastructure, or critical national security sites.
Implementation Roadmap: From Audit to Authorized
Audit Current Software Security Posture
Identify where facility data is currently hosted, who holds administrative access, and whether your existing platform meets your agency's encryption and data sovereignty standards. Most agencies discover their current CMMS is hosted on commercial cloud infrastructure without FedRAMP authorization — a FISMA compliance gap that affects every work order, every asset record, and every inspection log the system has ever processed.
Classify Your System and Define Mandatory Controls
Work with your IT and InfoSec teams to classify the CMMS under FIPS 199 — Low, Moderate, or High — based on the data it processes. Define your mandatory controls: SAML 2.0 SSO, AES-256 encryption, data residency requirements, PIV/CAC authentication, and audit log retention periods. These become the vendor evaluation criteria for your RFP or sole-source justification.
Evaluate Vendors Against FedRAMP Marketplace
Only "Authorized" status on the FedRAMP Marketplace satisfies FISMA's cloud requirement. "In Process" means assessment is underway — not that authorization exists. Verify the vendor's authorization level against your classified impact level. A Moderate-authorized vendor cannot serve a High-impact CMMS deployment. Request the vendor's System Security Plan (SSP) and continuous monitoring reports for your ATO package.
Deploy, Authorize, and Monitor Continuously
FISMA compliance is not a point-in-time achievement. The Risk Management Framework requires continuous monitoring — ongoing vulnerability scans, configuration reviews, access control audits, and annual security assessments. Your CMMS vendor must provide continuous monitoring reports that feed your agency's ATO renewal. Platforms built for government operations generate these reports automatically as a byproduct of normal operations. Sign up free to see OxMaint's continuous monitoring dashboard for government deployments.
Frequently Asked Questions
Does a government agency's CMMS need to be FedRAMP authorized?
Yes, if it is a cloud-based system that processes, stores, or transmits government data. OMB requires executive federal agencies to use FedRAMP-authorized cloud services for all federal data. State agencies managing federally funded programs and private contractors working with federal agencies are also subject to FISMA requirements, which FedRAMP authorization satisfies for cloud deployments. Using a non-FedRAMP cloud CMMS creates a FISMA compliance gap that can surface during IG audits and annual FISMA reporting. Book a demo to review OxMaint's authorization status for your procurement process.
What is the difference between FedRAMP Moderate and High for a CMMS?
FedRAMP Moderate (325 NIST 800-53 controls) applies to most civilian facility CMMS systems handling building security data, PII, and infrastructure records. FedRAMP High (421 controls) is required where a compromise would have severe or catastrophic consequences — military installations, classified research facilities, law enforcement infrastructure, and national security sites. The impact level is determined by your agency's FIPS 199 classification, not by the software vendor.
What CMMS data specifically creates FISMA compliance obligations?
Any CMMS data that, if compromised, could have an adverse effect on agency operations triggers FISMA classification. This includes building blueprints and layouts, access control and security system maintenance schedules, contractor personnel records and badging histories, critical infrastructure inspection results, and any PII associated with employees or visitors. The NIST SP 800-53 AU control family requires comprehensive audit logging of all access to this data — a requirement that many commercial CMMS platforms do not satisfy natively.
Can OxMaint support a government agency's ATO process?
Yes. OxMaint's government compliance team provides System Security Plan documentation, NIST 800-53 control mapping, continuous monitoring reports, and penetration test results to support your agency's Authority to Operate process. FedRAMP-aligned security documentation is available for review during the procurement evaluation phase — before your agency makes a platform commitment. Book a demo to access OxMaint's ATO support documentation for your InfoSec team.
Protect Your Facility Data with Government-Grade CMMS Security
OxMaint delivers FedRAMP-aligned, FISMA-ready maintenance management with AES-256 encryption, zero-trust architecture, PIV/CAC-compatible authentication, and automated compliance reporting — built for public sector agencies that cannot afford a security gap in their facility operations platform.