In 2021, attackers breached a water treatment facility in Oldsmar, Florida by exploiting remote access credentials in the plant's control system — and nearly raised sodium hydroxide to dangerous levels before an operator caught the change on screen. In 2022, a ransomware attack on a major manufacturing group locked their CMMS, ERP, and production systems simultaneously, costing an estimated $90 million in recovery costs and lost production. These aren't anomalies — they're the new baseline for industrial cyber risk. As maintenance systems become more connected — receiving data from IoT sensors, integrating with ERP platforms, enabling remote technician access, and storing decades of asset history — they become high-value targets for ransomware groups, nation-state actors, and opportunistic attackers. A CMMS breach isn't just an IT problem: it exposes maintenance schedules (helping attackers understand when facilities are vulnerable), equipment health data (revealing which assets are near failure), and access credentials that often connect directly to OT networks. Securing your maintenance platform isn't optional in an Industry 4.0 environment — it's a core operational requirement. This guide covers the threat landscape, the security architecture your CMMS must have, and the specific controls Oxmaint implements to protect industrial asset data across its customer base.
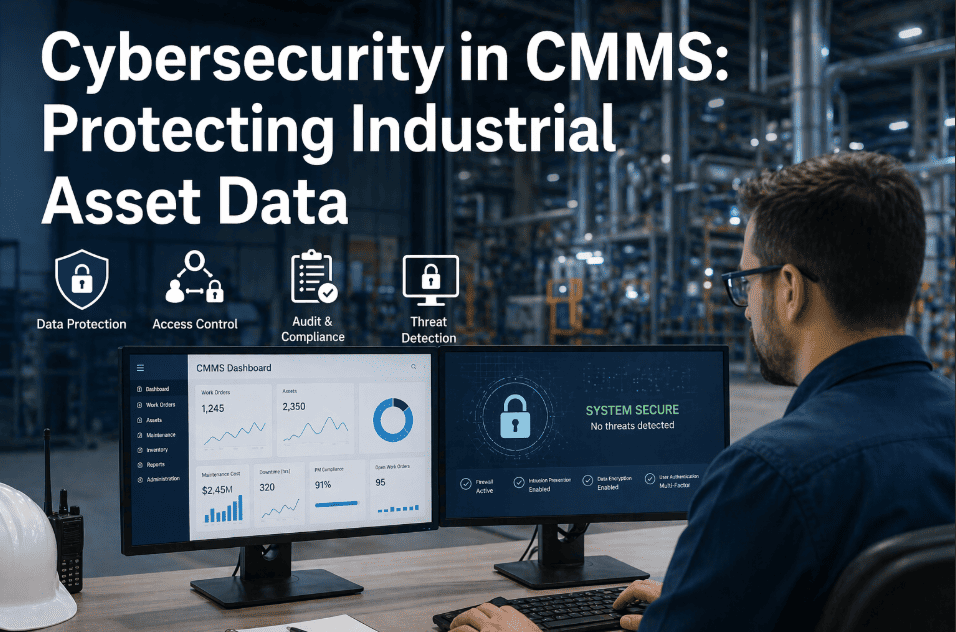
Cybersecurity in CMMS: Protecting Industrial Asset Data
Secure your maintenance platform against ransomware, credential theft, and OT network intrusion — with the specific security controls that industrial operations require in an Industry 4.0 environment.
How Attackers Target Maintenance Systems — The Real Threat Vectors
CMMS platforms are targeted differently from standard enterprise software because they sit at the intersection of IT and OT networks. Understanding the specific attack vectors maintenance systems face is the first step in building appropriate defenses.
Credential Stuffing via Remote Access
Maintenance technicians frequently use weak or reused passwords for remote CMMS access. Attackers obtain credential lists from other breaches and systematically test them against CMMS login portals — gaining access to maintenance schedules, asset layouts, and sometimes OT network connections.
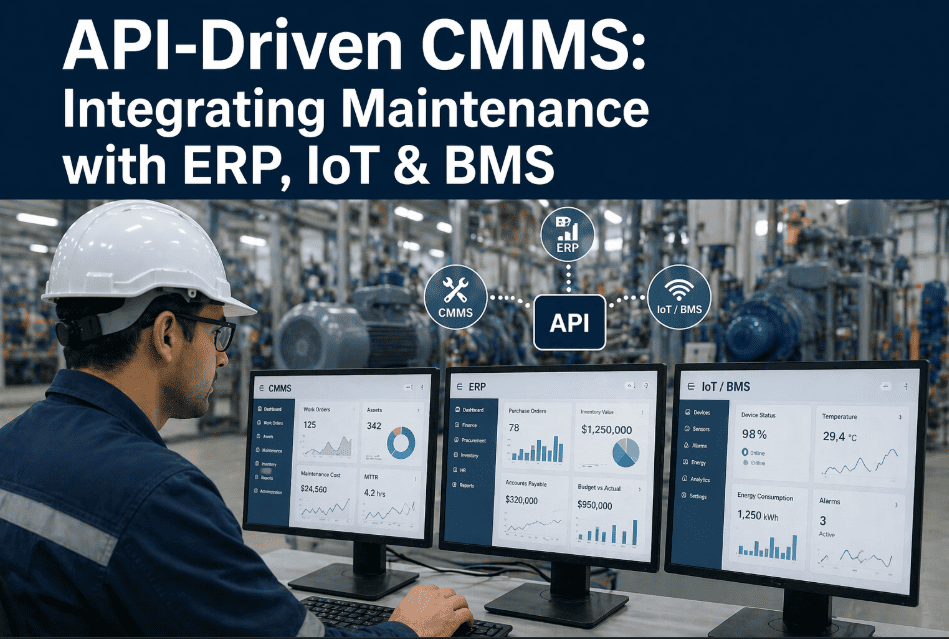
API Endpoint Exploitation
As CMMS platforms add API integrations, each endpoint becomes a potential attack surface. Poorly secured API keys, missing rate limiting, or excessive permission scopes allow attackers to exfiltrate asset data or inject malicious work orders through integration channels rather than the UI.
Ransomware via CMMS-OT Pivot
CMMS platforms that connect directly to OT networks for PLC data or BMS integration create a pivot point. Ransomware that enters through the CMMS can traverse the connection to OT systems, potentially taking down production lines or building systems along with the maintenance platform.
Insider Threat — Disgruntled Technicians
Maintenance staff with broad CMMS access can export asset lists, delete PM records, or modify calibration data before leaving. Without granular audit trails and access controls tied to job function, insider damage is difficult to detect and attribute.
The Security Controls Your CMMS Must Have in 2026
Industrial cybersecurity frameworks — NIST CSF, IEC 62443, and ISA/IEC 62443-2-1 — define security requirements for operational technology environments. A CMMS operating in these environments must meet specific controls at each layer. Here's the complete security architecture Oxmaint implements and what you should demand from any maintenance platform vendor.
Security-First CMMS for Industrial Operations
SOC 2 Type II certified, MFA enforced, TLS 1.3 encrypted, with full audit trails and immutable logs — Oxmaint is built for the security requirements of critical infrastructure environments.
Defense-in-Depth Security Model for Industrial CMMS
No single security control is sufficient — defense in depth means layering multiple independent controls so that a failure in one layer doesn't compromise the entire system. This is the security model Oxmaint implements across all customer deployments, and the model you should require from any CMMS vendor operating in industrial environments.
Layer 1 — Perimeter Security
WAF (Web Application Firewall), DDoS protection, IP allowlisting for OT network connections, CDN with threat intelligence. Blocks the majority of automated attack traffic before reaching the application.
Layer 2 — Identity Security
MFA enforcement for all users, SSO with enterprise identity providers, session timeout policies, geographic login anomaly detection, and automated account lockout on failed authentication attempts.
Layer 3 — Application Security
Role-based access control enforced at the application layer, input validation on all fields, parameterized database queries preventing SQL injection, OWASP Top 10 controls, and quarterly penetration testing.
Layer 4 — Data Security
AES-256 encryption at rest, TLS 1.3 in transit, tenant data isolation at the database level, field-level encryption for sensitive asset data, and automated backup with encrypted off-site storage.
Layer 5 — Monitoring & Response
24/7 SOC monitoring, SIEM integration, immutable audit logs with 1-year retention, real-time anomaly detection, and documented incident response procedures with sub-2-hour customer notification SLA.
CMMS Security Evaluation Checklist — What to Ask Every Vendor
When evaluating CMMS vendors for industrial environments, security documentation and certifications matter as much as features. Use this checklist during vendor evaluation. Any "No" answer on the critical items is a disqualifying factor for regulated industries and critical infrastructure operators.
"After the Colonial Pipeline incident, our CISO required every OT-adjacent system to pass a security review before renewal. Oxmaint was the only CMMS vendor that provided a SOC 2 Type II report, completed our security questionnaire in 48 hours, and could demonstrate MFA and RBAC controls in a live environment. The others sent marketing materials."
— Director of OT Security, natural gas pipeline operations, Texas
Frequently Asked Questions
Why is CMMS specifically a cybersecurity risk in industrial environments?
What's the minimum security certification I should require from a CMMS vendor?
How does CMMS-to-OT integration create cybersecurity risk?
Does Oxmaint support on-premise deployment for air-gapped environments?
How do I audit user activity in Oxmaint for a security investigation?
Maintenance Security That Meets Industrial Standards
SOC 2 Type II certified. MFA enforced. Full audit trail. Built for Industry 4.0.