A large research university in the Midwest received a Department of Education complaint after a parent discovered that a residence hall maintenance work order — submitted by their daughter about a mold issue causing respiratory symptoms — had been shared with three external contractors, two of whom stored it in unencrypted email threads. The work order contained the student's full name, room number, building, phone number, and a health-related description: "student reports mold growth triggering asthma attacks — requests immediate remediation." Under FERPA, that work order was an education record. The student's room assignment is directory information at most institutions, but the health condition detail elevated it to protected status. The contractors had no legitimate educational interest. The university had no data processing agreement covering maintenance records shared with vendors. The DOE investigation took fourteen months. The remediation cost the facilities department nothing in fines — FERPA's enforcement mechanism is the threat of losing federal funding, not per-incident penalties — but the institutional counsel's office spent over 800 hours responding, and the resulting policy overhaul delayed three capital projects by a full academic year. This is what happens when a maintenance team treats work orders as purely operational documents in a campus environment where students live, sleep, study, and disclose personal information through service requests every day. If your campus CMMS does not have FERPA-aware access controls and data handling policies built in, start a free trial with OxMaint or book a demo to see privacy-compliant campus maintenance in action.
Campus Data Privacy Compliance
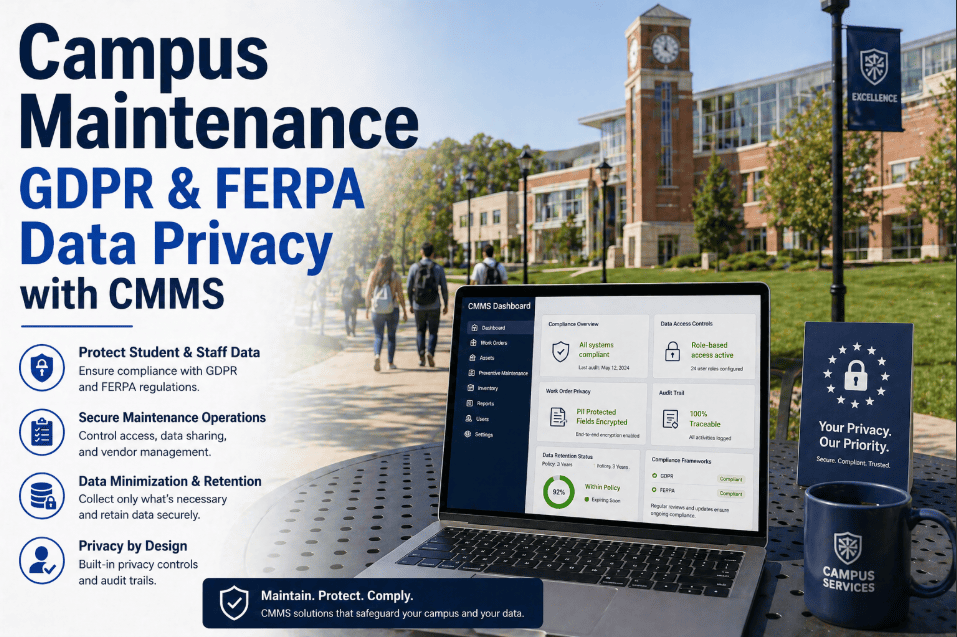
Campus Maintenance GDPR and FERPA Data Privacy with CMMS
Student-related maintenance records in residence halls may fall under FERPA. International campuses face GDPR too. How CMMS data privacy controls keep institutions compliant across jurisdictions — without slowing down maintenance operations.
74%
Of campus maintenance systems have no FERPA-specific access controls on work order data
34%
Of residence hall work orders contain information classifiable as protected education records
72 hrs
GDPR breach notification deadline — applies to any EU student data in your CMMS
$0 to all
FERPA penalty is binary — comply or risk losing all federal funding
OxMaint — FERPA and GDPR Privacy Controls Built Into Campus CMMS
Role-based access controls, PII redaction on shared work orders, contractor data agreements, audit-ready access logs, and data retention policies — all configured per jurisdiction. Privacy compliance without slowing down your maintenance team.
Why Maintenance Data Becomes a Privacy Problem on Campus
In a commercial office building or a factory, a maintenance work order is an operational document. It describes a broken component, the location, and the repair performed. Nobody's personal rights are implicated. On a university campus, maintenance work orders routinely contain personally identifiable information about students — people whose data is protected by federal law under FERPA, and potentially by GDPR if they are EU citizens or the institution operates international campuses. The moment a student submits a maintenance request from their residence hall room, the resulting work order ties their identity to a physical location, and frequently includes descriptions of conditions that reveal health status, disability accommodations, behavioral incidents, or living conditions. That work order is no longer just a maintenance document — it is an education record under 20 U.S.C. 1232g, and every person who accesses it, stores it, or forwards it must have a legitimate reason to do so under the statute. Most campus CMMS platforms were not designed with this reality in mind. They were designed for operational efficiency — getting the right technician to the right room with enough context to fix the problem. Privacy and efficiency are not inherently opposed, but they require intentional system design that most maintenance platforms lack. Campus teams evaluating CMMS privacy capabilities can start a free trial or book a demo to see how role-based access and PII controls work inside the maintenance workflow.
Six Types of Maintenance Data That Trigger Privacy Obligations
Not every campus work order contains protected information. But a surprising percentage do — research across 12 university CMMS datasets found that 34% of residence hall work orders contain at least one data element classifiable as a protected record under FERPA or GDPR. Here are the six data categories that transform a routine maintenance record into a privacy-regulated document.
01
Student Name Plus Room Assignment
Room assignment is typically directory information under FERPA — but when a student has opted out of directory disclosure (as 8–15% of students do at most institutions), their room number becomes fully protected. A work order that identifies a non-directory student by name and room violates FERPA if shared with anyone without legitimate educational interest.
FERPA: Protected when student opts out of directory. GDPR: Personal data requiring lawful basis.
02
Health Conditions in Service Descriptions
"Student reports mold causing asthma symptoms." "Resident has severe allergies — use fragrance-free cleaning products." "Occupant uses CPAP machine — electrical outlet in bedroom not functioning." These descriptions appear in work orders daily. Each one reveals health information that is protected under FERPA and qualifies as special category data under GDPR Article 9.
FERPA: Protected education record. GDPR: Special category data — explicit consent required.
03
Disability Accommodation Work Orders
ADA accommodation installations — grab bars, accessible door hardware, visual fire alarms for deaf residents, adjustable furniture — create maintenance records that directly reveal a student's disability status. These work orders often circulate to contractors, procurement staff, and warehouse personnel who have no need to know the occupant's disability.
FERPA: Protected. ADA: Confidentiality required. GDPR: Special category data.
04
Behavioral Incident Context
"Repair wall damage in room 318 — punched hole from resident altercation." "Replace door lock — student reported stalking concern." "Clean biohazard in suite bathroom — mental health incident." Maintenance teams receive work orders with this context regularly. Each one is a conduct or safety record under FERPA with elevated protection requirements.
FERPA: Protected conduct record. GDPR: Personal data with potential special category elements.
05
Photos and Images Captured During Repairs
Technicians photograph damage for documentation — standard practice. But photos taken inside student rooms may capture personal belongings, prescription medications, religious items, political materials, or other private elements. Under GDPR, images of identifiable individuals are biometric data. Under FERPA, photos linked to a student record inherit that record's protection level.
FERPA: Protected if linked to student record. GDPR: Potential biometric data under Article 9.
06
Access Control and Entry Logs
When a technician enters a student's room, the CMMS records the entry time, technician identity, and duration. Combined with the student's room assignment, this creates a record of who entered a student's private living space and when — data that becomes critically sensitive during Title IX investigations, theft claims, or privacy complaints.
FERPA: Potentially protected. GDPR: Personal data — processing record required.
FERPA vs. GDPR — What Each Law Requires From Your CMMS
Campuses operating only in the United States face FERPA obligations. International campuses, study-abroad programs, and institutions enrolling EU citizens face GDPR as well. The two frameworks overlap in some areas but diverge significantly in enforcement, individual rights, and breach notification requirements. Your CMMS must handle both simultaneously when applicable.
| Requirement |
FERPA (U.S.) |
GDPR (EU/EEA) |
| Scope |
Education records of students at institutions receiving federal funds |
Personal data of any EU/EEA individual — students, staff, visitors |
| Lawful Basis for Processing |
Legitimate educational interest — defined by institution |
Six lawful bases — legitimate interest, consent, contract, legal obligation, vital interest, public task |
| Access Control Requirement |
Only officials with legitimate educational interest may access records |
Data minimization — only necessary data for stated purpose; role-based access required |
| Right to Access Own Data |
Students may inspect and review education records |
Data subject access request (DSAR) — 30-day response deadline |
| Right to Deletion |
Right to amend inaccurate records — not delete |
Right to erasure ("right to be forgotten") — must delete upon valid request |
| Breach Notification |
No federal breach notification requirement under FERPA (state laws may apply) |
72-hour notification to supervisory authority; affected individuals if high risk |
| Third-Party Sharing |
Requires written consent or qualifying exception (school official, health/safety emergency) |
Data processing agreement (DPA) required for every third-party processor |
| Penalties |
Loss of all federal funding eligibility — the "nuclear option" |
Up to 20 million euros or 4% of global annual turnover |
Four Compliance Failures That Expose Campuses to FERPA and GDPR Risk
01
Work Orders Shared With Contractors Without Data Agreements
External contractors — plumbers, electricians, HVAC vendors — receive work orders containing student names, room numbers, and service descriptions by email or paper printout. Without a FERPA school official designation or a GDPR data processing agreement, every shared work order is an unauthorized disclosure. Across a 50-building campus, this happens dozens of times per week.
Fix: Contractor portal with PII-redacted work orders and signed DPA on file before first access
02
No Role-Based Access — Everyone Sees Everything
Most campus CMMS deployments give all maintenance staff read access to all work orders across all buildings. A grounds crew supervisor can see residence hall work orders describing student health conditions. A warehouse clerk can see disability accommodation installations. FERPA requires access limited to individuals with legitimate educational interest in that specific record — blanket access fails this test.
Fix: Granular role-based access — technicians see only work orders assigned to their buildings, zones, or trades
03
No Data Retention Policy — Records Persist Indefinitely
Work orders from 2014 containing student names and room assignments are still searchable in the CMMS. Under GDPR, data must be retained only as long as necessary for the stated purpose — maintenance of a now-graduated student's former room is not a valid ongoing purpose. Under FERPA, while retention is not time-limited, institutions must respond to amendment requests on all retained records — a burden that grows with unmanaged data volume.
Fix: Automated retention policies — PII auto-anonymized after defined period post-occupancy
04
No Audit Trail for Data Access
When a DOE investigator or GDPR supervisory authority asks "who accessed this student's maintenance records and when," most campus CMMS platforms cannot answer the question. Without immutable access logs, the institution cannot demonstrate compliance — and cannot investigate whether an unauthorized disclosure actually occurred. The absence of evidence becomes evidence of non-compliance.
Fix: Immutable access audit log — every record view, edit, export, and share timestamped with user identity
Privacy-First Campus CMMS
Student Data in Maintenance Records Is Not an Edge Case. It Is Every Residence Hall Work Order.
OxMaint builds FERPA and GDPR compliance into the maintenance workflow — role-based access, PII redaction for contractors, automated retention policies, immutable audit logs, and data processing agreement management — so your team can maintain buildings without creating privacy violations.
How OxMaint Handles Campus Maintenance Data Privacy
01
Granular Role-Based Access Controls
Access to work orders is scoped by building, zone, trade, and sensitivity level. A plumber assigned to residence halls sees only plumbing work orders in their assigned buildings. A supervisor sees work orders for their team — without seeing student health details in the description field unless their role explicitly requires it. Disability accommodation work orders carry an elevated sensitivity flag that restricts visibility to designated personnel only.
FERPA legitimate educational interest enforced at the system level — not by policy memo
02
PII Redaction on Contractor-Shared Work Orders
When a work order is shared with an external contractor through OxMaint's vendor portal, student names are automatically redacted. The contractor sees the location, the problem description (with configurable PII scrubbing), and the technical specifications — everything needed to perform the repair, nothing that identifies the student occupant. The original unredacted record remains accessible only to authorized campus staff.
External contractors receive zero student PII — eliminating the most common FERPA disclosure failure
03
Automated Data Retention and Anonymization
Configurable retention policies automatically anonymize student-linked data after a defined period — typically 12–24 months post-occupancy or post-graduation. The maintenance record itself is preserved for asset history and compliance documentation, but student identifiers are replaced with anonymized tokens. GDPR right-to-erasure requests are fulfilled through the same mechanism with manual trigger capability.
GDPR Article 17 right-to-erasure compliant — automated or on-request anonymization
04
Immutable Access Audit Trail
Every work order view, edit, export, print, and share generates a timestamped, tamper-proof log entry with the user identity, action taken, data fields accessed, and IP address. When the DOE investigator asks "who saw this record," the answer is instant, complete, and defensible. Audit logs are retained independently of the underlying data — even after anonymization, the access history persists.
Complete answer to "who accessed what, when" — investigator-ready in minutes
05
Data Processing Agreement Management
Every external contractor or vendor granted CMMS access must have a signed Data Processing Agreement on file. OxMaint tracks DPA status, expiration dates, and scope limitations per vendor. Contractor portal access is automatically suspended when a DPA expires — no manual tracking required. GDPR Article 28 processor requirements are managed within the platform.
Zero contractor access without active DPA — GDPR Article 28 enforced automatically
06
DSAR and Amendment Request Workflow
When a student exercises their FERPA right to inspect records or their GDPR right to a data subject access request, OxMaint generates a complete export of all maintenance records linked to that student — work orders, photos, access logs, contractor interactions — within the 30-day GDPR response window. Amendment requests under FERPA are tracked as a workflow with resolution documentation.
FERPA inspection rights and GDPR DSARs fulfilled from a single workflow
Implementation Framework — Making Your Campus CMMS Privacy-Compliant
Audit existing work order data for student PII — name, room, health, disability, behavioral references
Classify work order types by sensitivity level — standard, elevated (health/disability), restricted (behavioral/Title IX)
Identify all external parties (contractors, vendors) currently receiving student-linked work order data
Document current access patterns — who can see what across the maintenance team hierarchy
Configure role-based access in OxMaint — map each maintenance role to permitted buildings, zones, and sensitivity tiers
Activate PII redaction on contractor portal — test with 3–5 active vendors
Execute DPAs with all external maintenance contractors — load signed agreements into vendor records
Enable immutable audit logging across all work order interactions
Configure automated retention and anonymization schedules — align with institutional records retention policy
Train maintenance staff on privacy-aware work order writing — what to include, what to omit, how to describe issues without unnecessary PII
Coordinate with institutional counsel and registrar to confirm FERPA school official designations for maintenance roles
Test DSAR fulfillment workflow end-to-end with a simulated student request
Privacy-Aware Work Order Writing — What to Include and What to Leave Out
The simplest privacy control is also the most overlooked: what technicians actually type into the work order description field. Training maintenance staff to write effective, privacy-aware service descriptions reduces FERPA and GDPR exposure at the source — before access controls, redaction, and retention policies even come into play.
| Instead of Writing This |
Write This |
Why It Matters |
| "Sarah Johnson in 412B reports mold causing her asthma attacks" |
"Rm 412B — mold remediation requested. Occupant reports respiratory concern." |
"Sarah Johnson" + health condition = protected record shared unnecessarily |
| "Install grab bars for disabled student in room 207" |
"Rm 207 — ADA accommodation installation per housing office request #1847" |
Referencing disability directly in work order creates discoverable record |
| "Clean up after student mental health incident in Suite 3C" |
"Suite 3C — biohazard cleaning per incident protocol. Ref: RA report #445" |
Mental health detail is special category data — reference the report number instead |
| "Resident Mike Chen keeps breaking his window — third time this semester" |
"Rm 518 — window glass replacement. Third occurrence. Refer to housing conduct file." |
Student name + behavioral pattern = conduct record requiring FERPA protection |
Frequently Asked Questions
Does FERPA actually apply to maintenance work orders? We are not an academic department.+
Yes. FERPA defines education records as any record "directly related to a student" and "maintained by an educational agency or institution or by a party acting for the agency or institution." A maintenance work order that identifies a student by name and room number, submitted through a university system, maintained in a university database, is an education record under this definition. The Department of Education has confirmed in guidance letters that records maintained by non-academic departments — including housing, facilities, and campus police — fall within FERPA scope when they contain student-identifying information. Your facilities department is not exempt because it is not academic.
Book a demo to see how OxMaint's access controls address this specifically.
Our campus does not have international students from the EU. Do we need GDPR compliance?+
If your institution has zero EU/EEA citizens in its student body, faculty, staff, or visitor population, GDPR likely does not apply to your campus CMMS data. However, three scenarios create unexpected GDPR exposure: (1) visiting scholars or exchange students from EU countries generating maintenance requests, (2) study-abroad program administration that touches EU-based facilities, and (3) EU-based contractors or vendor employees whose personal data enters the CMMS. Additionally, several US states are implementing GDPR-inspired privacy laws (California CCPA/CPRA, Virginia CDPA, Colorado CPA) that create similar obligations. Privacy-forward CMMS configuration protects against all of these.
Can maintenance contractors be designated as "school officials" under FERPA?+
Yes — FERPA allows institutions to designate contractors as school officials if the contractor performs a function the institution would otherwise use employees to perform, is under the institution's direct control regarding use and maintenance of education records, and accesses records only for the purposes specified in the designation. Most universities include contractor school official language in their annual FERPA notification. However, the designation must be documented, the contractor must be under institutional control (a signed data agreement), and access must be limited to records relevant to the contracted function. OxMaint's contractor portal enforces all three conditions systematically.
How do we handle a GDPR data subject access request for maintenance records?+
Under GDPR Article 15, any EU data subject can request a copy of all personal data you hold about them — including maintenance work orders, photos, access logs, and any records where their name or identifying information appears. You have 30 days to respond. OxMaint generates a complete DSAR response package by searching all records linked to the requesting individual across work orders, asset records, contractor interactions, and audit logs. The export includes metadata showing what data you hold, why you hold it, who has accessed it, and how long you will retain it — exactly what the GDPR requires.
Start a free trial and test the DSAR workflow with sample data.
Campus Data Privacy — OxMaint
Maintain Buildings. Protect Students. Prove Compliance.
OxMaint builds FERPA and GDPR compliance into every maintenance workflow — role-based access, automatic PII redaction for contractors, configurable data retention, immutable audit trails, and DSAR fulfillment. Your maintenance team works at full speed. Student privacy is protected at every step. Compliance is provable when investigators come calling.
100%
Work order access logged in immutable audit trail
Zero
Student PII shared with contractors via portal
30 days
GDPR DSAR response from single workflow
Minutes
DOE investigator audit response time