The healthcare industry stands at a critical crossroads. While medical technology advances at unprecedented speeds, the infrastructure supporting these innovations often remains trapped in decades past. Legacy systems—outdated software, aging hardware, and obsolete operating systems—have become the Achilles' heel of hospital cybersecurity, creating vulnerabilities that cybercriminals eagerly exploit. With 73% of healthcare providers still dependent on outdated systems and the average data breach costing $9.77 million, the question isn't whether legacy infrastructure poses a risk—it's how long hospitals can afford to ignore the inevitable.
Why Legacy Systems Are the Silent Catalyst Behind Hospital Downtime
Understanding the hidden connection between aging infrastructure and catastrophic cybersecurity failures
The Anatomy of a Legacy System Crisis
Legacy systems in healthcare aren't merely old computers running Windows XP in forgotten corners of the hospital. They represent a complex ecosystem of interconnected vulnerabilities that span electronic health records (EHRs), medical devices, network infrastructure, and administrative platforms. These systems were designed in an era when cybersecurity meant physical locks on server rooms, not sophisticated ransomware attacks that can encrypt entire hospital networks in minutes.
The Change Healthcare cyberattack of early 2024 served as a wake-up call for the entire industry. Affecting nearly 70% of US providers and payers, this single incident demonstrated how legacy infrastructures—characterized by fragmented EHR integrations and lack of unified security strategies—can bring healthcare operations to a grinding halt. Sign up today to discover how centralized maintenance platforms can prevent such catastrophic failures.
The Legacy System Risk Escalation Timeline
Year 1-3: Integration Strain
New technologies struggle to communicate with aging infrastructure. Data silos emerge, forcing staff to manually bridge gaps between systems, increasing error rates and delaying critical patient care decisions.
Year 4-6: Security Patch Gaps
Vendors stop supporting older software versions. Critical security patches no longer available, creating exploitable entry points that sophisticated threat actors actively scan for and target.
Year 7+: Critical Vulnerability
Systems become incompatible with modern security protocols. Ransomware attacks increase by 264%, with recovery costs exceeding $10 million per breach and patient safety directly compromised.
Why Hospitals Can't Simply "Update Everything"
The path from legacy to modern infrastructure isn't as simple as installing new software. Healthcare organizations face unique constraints that complicate modernization efforts:
Regulatory Compliance Burden
HIPAA requirements, FDA validations for medical devices, and state healthcare regulations create a complex web of compliance that must be maintained during any transition. A single misstep can result in millions in penalties.
24/7 Operational Reality
Hospitals cannot simply "shut down for maintenance." Patient care continues around the clock, making system migrations incredibly complex. Emergency rooms must remain open, surgeries must proceed, and critical care cannot pause.
Interoperability Requirements
New systems must seamlessly integrate with existing EHRs, lab systems, and medical devices—many of which use proprietary protocols from the 1990s. Breaking these connections risks disrupting life-saving workflows.
Budget Constraints
With thin operating margins, many hospitals allocate just 4-6% of budgets to IT, leaving little room for comprehensive modernization. CFOs must balance infrastructure investment against immediate patient care needs.
These challenges explain why 65% of healthcare systems view legacy technology as their biggest IT challenge, despite 75% of providers increasing IT spending. The solution isn't just spending more—it's spending smarter. Book a demo to see how intelligent asset management transforms infrastructure risk into operational resilience.
Transform Your Infrastructure Risk Into Operational Resilience
Don't let legacy systems dictate your hospital's vulnerability profile. Every unpatched server, every outdated medical device, and every unsupported operating system represents a potential entry point for attackers who see healthcare organizations as high-value, high-vulnerability targets.
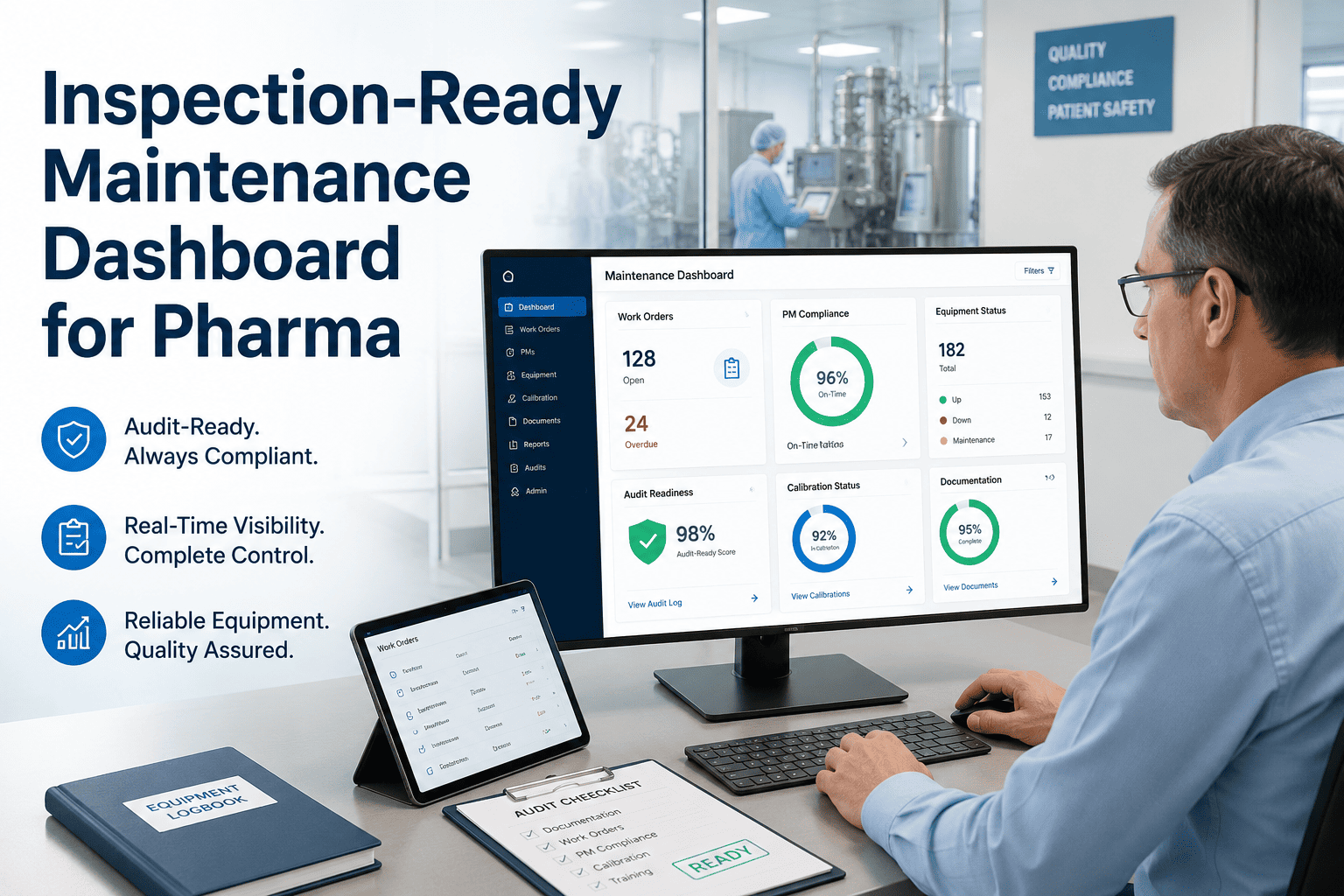
Oxmaint's centralized maintenance platform provides real-time visibility into your entire infrastructure, identifying aging assets before they become security liabilities. Our healthcare-specific solution tracks end-of-life dates, monitors patch compliance, and prioritizes replacement schedules based on clinical criticality and risk exposure.
Hospitals using Oxmaint report 40% faster incident response times and 60% reduction in unplanned downtime. Our automated workflows ensure that no critical system falls through the cracks, while our compliance dashboards keep you audit-ready 24/7. From MRI machines running Windows 7 to EHR servers approaching end-of-support, Oxmaint gives you the visibility and control needed to modernize without disrupting patient care.
The Hidden Costs Beyond the Breach
When discussing legacy system risks, the conversation often focuses on direct breach costs—the $9.77 million average, the ransom payments, the regulatory fines. But the true cost extends far beyond these visible line items:
The Ascension ransomware attack of 2024 illustrated this perfectly. Disrupting 140 hospitals with expected recovery costs of $1.1–1.6 billion, the incident wasn't just a technical failure—it was an operational catastrophe that forced providers to revert to paper records, increasing medical error risks and treatment delays. When 83% of healthcare organizations have experienced a breach in the past two years, the question shifts from "if" to "when"—and more importantly, "how prepared are we?"
Medical Devices: The Forgotten Attack Vector
Perhaps the most insidious legacy risk lies not in administrative computers but in medical devices themselves. MRI machines, infusion pumps, and diagnostic equipment often outlive their software support by decades. The FDA may approve continued use based on hardware safety, even when the underlying operating systems—sometimes Windows variants from the early 2000s—no longer receive security patches.
This creates a paradox: clinically safe but digitally dangerous equipment. An MRI machine might perform perfectly for imaging, but its network-connected control system running an unpatched Windows version becomes an open door for attackers. Once inside, ransomware can spread laterally, encrypting patient records, scheduling systems, and billing platforms. Start your free trial to discover how comprehensive asset inventory prevents such blind spots.
Critical Insight
Medical devices often run on operating systems that vendors no longer support, yet remain connected to hospital networks. Each unpatched device represents a potential entry point for sophisticated cyberattacks that can move laterally through your infrastructure.
Building a Resilient Infrastructure Strategy
Modernizing healthcare infrastructure doesn't require ripping and replacing every legacy system overnight. Instead, successful organizations adopt a phased, risk-based approach that prioritizes critical vulnerabilities while maintaining operational continuity.
Comprehensive Asset Discovery
You cannot protect what you cannot see. Complete visibility into all connected devices, software versions, and network endpoints is the foundation of security. Oxmaint automatically discovers and catalogs every asset.
Risk-Based Prioritization
Not all legacy systems pose equal risk. Prioritize modernization based on data sensitivity, network exposure, and criticality to patient care. Focus limited resources on highest-impact vulnerabilities first.
Network Segmentation
Isolate legacy systems that cannot be immediately replaced. Zero Trust Architecture ensures that even if one segment is compromised, the breach doesn't spread to critical patient care systems.
Continuous Monitoring
Legacy systems require enhanced monitoring. Real-time anomaly detection identifies unusual patterns that indicate compromise attempts before they escalate into full breaches.
The HHS Cybersecurity Performance Goals (CPGs) provide a framework for these efforts, offering voluntary but essential guidelines for healthcare organizations. However, guidelines alone don't prevent breaches—execution does. Book your consultation to learn how Oxmaint operationalizes these security frameworks into daily workflows.
See How Centralized Maintenance Reduces Security Exposure
Hospitals using Oxmaint report 40% faster incident response times and 60% reduction in unplanned downtime. Our platform transforms infrastructure management from a cost center into a strategic advantage that protects both your bottom line and your patients.
The ROI of Proactive Infrastructure Management
When calculating the return on infrastructure modernization, hospitals must look beyond IT budgets to operational efficiency. The U.S. federal healthcare system alone spends approximately $337 million annually just maintaining outdated platforms—funds that could modernize infrastructure and improve compliance with current security standards.
Consider the alternative costs: CommonSpirit Health's 2022 attack cost $160 million. Scripps Health lost $112.7 million after a 2021 breach. These figures don't include the immeasurable cost of delayed cancer treatments, postponed surgeries, and diverted emergency patients. When downtime averages $2 million per day with recovery periods exceeding 17 days, the math becomes clear—investing in modern infrastructure management isn't an expense, it's insurance against catastrophic loss.
Modern platforms like Oxmaint shift the paradigm from reactive firefighting to proactive risk management. By centralizing asset visibility, automating maintenance schedules, and providing real-time vulnerability assessments, hospitals can identify aging infrastructure before it becomes a breach vector. Sign up now to start your infrastructure risk assessment.
Frequently Asked Questions
What qualifies as a "legacy system" in healthcare?
Legacy systems include any hardware, software, or medical devices that are no longer supported by vendors, cannot receive security updates, or use obsolete operating systems. This ranges from Windows XP-based administrative computers to MRI machines running embedded software from the early 2000s. The key risk factor is the inability to patch known vulnerabilities while remaining connected to hospital networks.
Why can't hospitals simply disconnect legacy systems from the internet?
Modern healthcare requires connectivity. EHR systems need to communicate with labs, pharmacies, and insurance networks. Medical devices transmit data to central monitoring stations. Telehealth requires internet access. Complete disconnection would cripple modern care delivery. The solution is controlled connectivity with robust segmentation and monitoring, not isolation.
How does Oxmaint help reduce cybersecurity risks from legacy infrastructure?
Oxmaint provides centralized visibility into your entire infrastructure portfolio, identifying aging assets, tracking end-of-life dates, and prioritizing replacement schedules based on risk exposure. By maintaining comprehensive asset inventories and automating maintenance workflows, hospitals can identify vulnerable legacy systems before attackers do. Book a demo to see the platform in action.
What is the average timeline for legacy system modernization?
Timelines vary based on hospital size and complexity, but most organizations benefit from a 3-5 year phased approach. Immediate priorities include network segmentation and enhanced monitoring of critical legacy systems. Medium-term goals focus on replacing end-of-life administrative platforms. Long-term strategies address medical device modernization. Oxmaint helps organizations plan and execute these phases without disrupting patient care.
Are small hospitals and clinics at the same risk as large health systems?
Smaller providers often face heightened risk due to limited IT budgets and cybersecurity expertise. While they may have fewer total endpoints, they often lack dedicated security staff and rely heavily on outsourced IT with limited visibility into legacy vulnerabilities. Ransomware groups specifically target smaller providers assuming weaker defenses. The HHS Cybersecurity Performance Goals provide scaled guidance for organizations of all sizes.
How do we maintain HIPAA compliance during system modernization?
HIPAA compliance must be maintained throughout any modernization effort. This requires thorough risk assessments before changes, business associate agreements with vendors, encrypted data transmission during migrations, and comprehensive audit trails. Modernization actually improves long-term HIPAA compliance by replacing systems that cannot meet current encryption and access control standards.
Stop Gambling with Your Hospital's Infrastructure Security
Every day legacy systems remain unmonitored is another day of unnecessary risk. Healthcare organizations that adopt proactive infrastructure management don't just prevent breaches—they build operational resilience that supports better patient care.
Join 500+ healthcare facilities already using Oxmaint to transform infrastructure risk management.