Modern steel plants are no longer isolated facilities running on mechanical instinct—they are deeply connected ecosystems of sensors, PLCs, SCADA systems, and maintenance platforms that share data across operational technology (OT) and IT networks. That connectivity drives efficiency, but it also opens attack surfaces that threat actors are actively exploiting. A single ransomware intrusion into a maintenance management system can freeze production lines, corrupt critical asset data, and trigger regulatory consequences that take months to resolve. Schedule a free OT security review with our team and find out exactly where your connected plant is most exposed—and what to fix first.
Why OT Cybersecurity Is a Critical Priority for Steel Manufacturers
Steel production environments combine decades-old control systems with modern cloud-connected maintenance platforms, creating a patchwork of legacy and contemporary technology that is extremely difficult to secure uniformly. Attackers understand this. Industrial control system attacks have surged globally, and heavy manufacturing—including steel—ranks among the most targeted sectors. The consequences of a successful breach go far beyond data theft: they include physical damage to equipment, environmental incidents, and production halts that dwarf the cost of any ransom demand.
$4.7M
Average cost of an industrial cybersecurity incident in manufacturing, including downtime, remediation, and regulatory penalties
73%
Of OT environments have vulnerabilities that could allow attackers to move from IT networks into production control systems
6x
Increase in cyberattacks targeting industrial control systems and OT environments over the past five years
Key Insight
A steel plant's blast furnace, rolling mill, and continuous caster are now software-controlled assets. If the OT network that manages them is breached, attackers can manipulate process parameters, falsify sensor readings, or disable safety interlocks—creating hazards that go far beyond financial loss.
The Unique OT Security Challenges in Steel Plant Environments
Securing a steel plant's operational technology is fundamentally different from securing a corporate IT network. The constraints, architectures, and failure consequences demand a specialized approach that most general cybersecurity frameworks do not fully address.
Many steel plants operate PLCs, HMIs, and SCADA systems that are ten to thirty years old, running operating systems no longer supported by vendors. These systems cannot be patched on a standard IT cadence—often they cannot be patched at all without risking process disruption. Yet they are increasingly connected to modern networks for remote monitoring and maintenance integration.
Implication: Compensating controls—network segmentation, application whitelisting, and unidirectional data gateways—must replace patching as the primary defense for legacy OT assets.
CMMS platforms, predictive maintenance tools, and ERP integrations create bidirectional data flows between business networks and plant floor systems. Each integration point is a potential pivot for an attacker who has compromised the corporate IT environment. Without strict zone controls, a phishing email targeting a maintenance planner can become a pathway to the process control network.
Implication: Every IT-to-OT data connection must be documented, minimized, and protected with strong authentication and encrypted channels. Zero-trust principles apply at every integration boundary.
Equipment OEMs, automation vendors, and maintenance contractors routinely require remote access to steel plant systems for diagnostics, updates, and support. Unmanaged remote access credentials and always-on VPN tunnels represent some of the highest-risk entry points in industrial environments. Several major industrial attacks in recent years originated through compromised vendor credentials.
Implication: All third-party remote sessions must use privileged access management, time-limited credentials, and full session recording. Permanent remote access tunnels should be eliminated where possible.
5 Core Cybersecurity Controls for Connected Steel Plant OT Networks
Effective OT security does not require replacing every legacy system or deploying enterprise security stacks on the plant floor. It requires applying the right controls in the right sequence, prioritized by actual risk to production continuity and personnel safety.
1
Implement Network Segmentation and the Purdue Model
Divide your plant network into clearly defined zones: enterprise IT, demilitarized zone (DMZ), supervisory control, and field device levels. Use industrial firewalls and data diodes to enforce strict communication rules between zones. Traffic between the business network and OT environment should flow through the DMZ only, never directly. This single architectural control stops the majority of lateral movement attacks that have crippled industrial facilities worldwide.
2
Build a Complete OT Asset Inventory
You cannot protect what you cannot see. Conduct a full discovery of every OT asset: PLCs, HMIs, engineering workstations, network switches, IP cameras, and smart sensors. Document firmware versions, communication protocols, vendor support status, and network connections for each device. A current and accurate OT asset inventory is the foundation of every other security control and is required by most industrial security standards including IEC 62443 and NIST SP 800-82.
3
Harden Maintenance Management System Integrations
CMMS platforms that connect to OT systems for asset data, sensor readings, and work order triggering must be treated as high-risk integration points. Enforce multi-factor authentication on all CMMS accounts, restrict API access to named IP addresses, encrypt all data in transit, and conduct quarterly access reviews to remove stale accounts. Every user account connecting a maintenance system to plant floor data is a credential that attackers will target.
4
Deploy OT-Specific Threat Detection and Monitoring
Standard IT security information and event management (SIEM) tools do not understand industrial protocols like Modbus, DNP3, or PROFINET. Deploy passive OT network monitoring solutions that establish behavioral baselines for your process systems and alert on anomalous commands, unexpected device communications, or unauthorized configuration changes. Passive monitoring is critical because active scanning can crash fragile legacy OT devices.
5
Develop and Test an OT-Specific Incident Response Plan
A cyber incident in a steel plant is not handled the same way as a corporate data breach. Your incident response plan must address process isolation procedures, manual fallback operations, safety system verification, and regulatory notification requirements. Run tabletop exercises at least annually with both IT security and operations personnel present. Teams that rehearse together respond faster and make fewer critical errors under pressure.
Secure Your Maintenance Systems Without Disrupting Operations
Oxmaint is built with industrial security in mind—role-based access control, encrypted data flows, full audit trails, and integration architectures designed for OT environments. Protect your plant without slowing your team down.
Securing CMMS and Maintenance Platforms in OT Environments
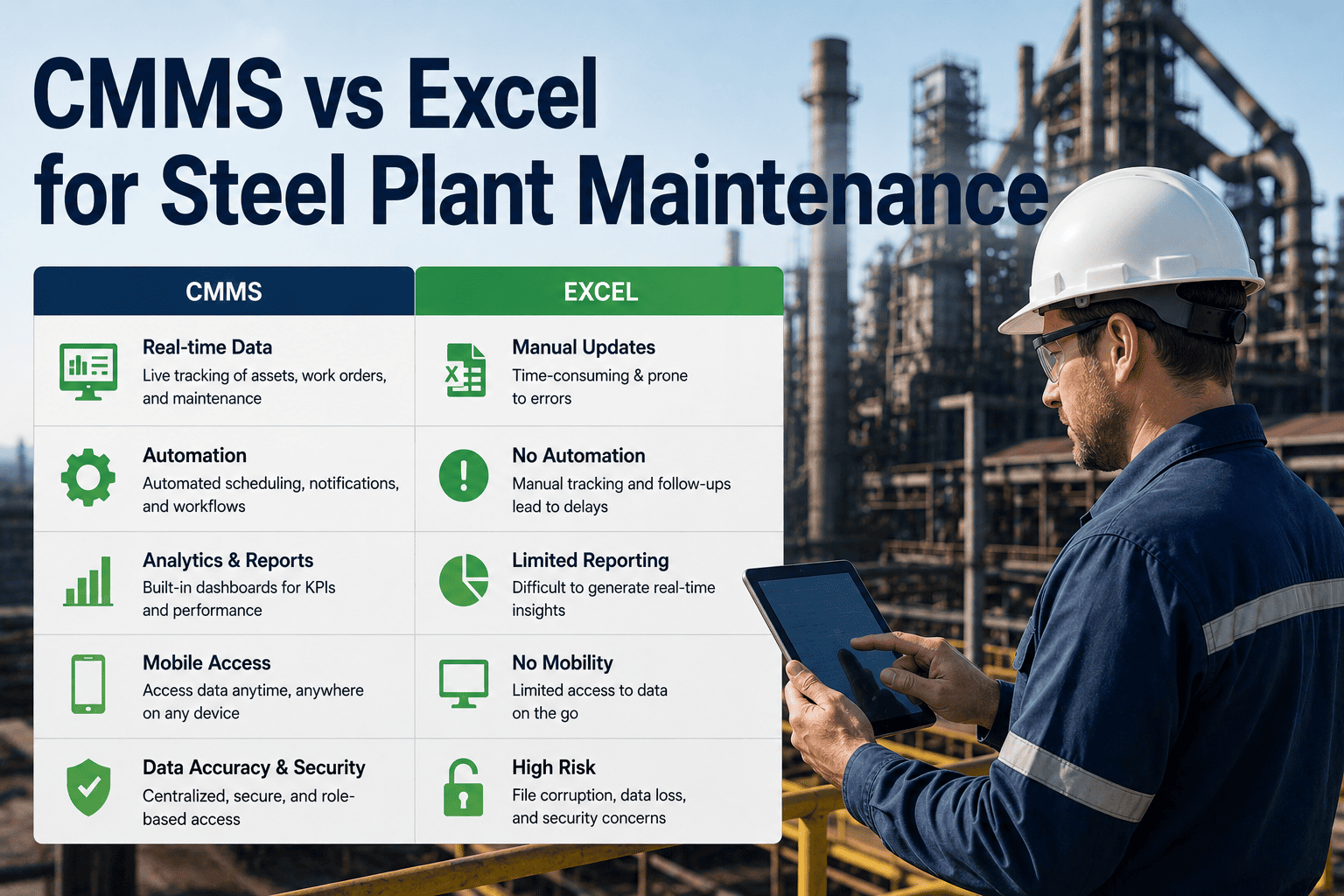
Computerized maintenance management systems sit at the intersection of IT and OT—they pull asset data from sensors and control systems while pushing work orders and parts information to plant floor teams. This dual connectivity makes them both strategically valuable and uniquely vulnerable. Securing a CMMS in a steel plant environment requires attention to identity, access, data, and integration architecture simultaneously.
Unsecured CMMS Risks
Shared login credentials across maintenance teams
No audit trail for work order changes or parts access
Direct database connections to OT historian systems
Vendor accounts active indefinitely after project completion
Maintenance data stored unencrypted on local servers
68%
of industrial breaches involve compromised credentials or access control failures
Secured CMMS Practices
Individual named accounts with role-based permissions
Immutable audit logs for every transaction and change
Read-only API connections via DMZ to OT data sources
Time-limited vendor credentials with session recording
End-to-end encryption with cloud or on-premise isolation
82%
reduction in unauthorized access incidents with MFA and role-based access controls
What to Look for in Cybersecurity-Ready Maintenance Software for Steel Plants
Not all CMMS platforms are built to operate securely in OT-adjacent environments. Steel plant operations managers and IT security teams should evaluate maintenance software against a specific set of security capabilities before deployment or renewal.
Role-Based Access Control
Granular permissions that limit each user to only the assets, work orders, and data required for their role. Operators see their equipment; planners see schedules; administrators control configuration.
Multi-Factor Authentication
MFA on every account eliminates the risk of credential theft enabling unauthorized access. Critical in environments where phishing attacks specifically target maintenance personnel with OT system access.
Immutable Audit Logging
Every work order update, parts transaction, asset modification, and login event captured in tamper-resistant logs. Essential for incident investigation and compliance with industrial security frameworks.
Encrypted Data Transmission
All data moving between the CMMS platform, mobile devices, and OT data sources must travel over encrypted channels. Unencrypted maintenance data on plant networks is a surveillance risk and a compliance failure.
On-Premise or Private Cloud Deployment
Sensitive maintenance and OT asset data should remain within your network perimeter or a dedicated private cloud instance. Multi-tenant SaaS platforms raise data residency and isolation concerns for regulated industries.
Vendor Access Management
Purpose-built controls for third-party technician access: time-limited sessions, scoped permissions, full activity logging, and instant revocation. No permanent vendor backdoors that persist after project completion.
Industry Standard
IEC 62443 is the leading international standard for industrial cybersecurity. Steel plants pursuing compliance require maintenance and OT systems that support zone-based security architectures, authenticated data flows, and comprehensive audit capabilities—features built into Oxmaint's industrial deployment options.
OT Cybersecurity KPIs Every Steel Plant Security Team Should Track
Industrial cybersecurity programs need measurable metrics to demonstrate improvement, justify investment, and identify gaps before attackers do. These indicators give operations and security leaders a shared language for assessing OT security posture across the plant.
Common OT Cybersecurity Mistakes in Steel Plant Environments
Even security-conscious organizations repeat the same OT mistakes because industrial environments operate under constraints that push security decisions in the wrong direction. Recognizing these patterns before they become incidents is the fastest way to strengthen your plant's security posture.
01
Treating OT Security as an IT Problem
IT security teams applying enterprise frameworks to OT environments without understanding process constraints often deploy controls that crash production systems or get bypassed by operations teams to maintain uptime.
02
Relying on Air Gaps That No Longer Exist
Many steel plants believe their OT networks are isolated, but remote access tools, USB drives, and cloud CMMS integrations have quietly eliminated those gaps. Assuming isolation that does not exist is more dangerous than acknowledging connectivity.
03
Skipping Security Reviews for Maintenance Software Updates
CMMS updates, integration changes, and new vendor connections alter the security posture of the entire OT-adjacent environment. Without a formal change review process, security controls can be inadvertently disabled by routine software updates.
04
No Backup and Recovery Plan for OT Systems
Ransomware targeting OT environments exploits the absence of tested recovery procedures. PLC configurations, HMI screen definitions, and historian databases must be backed up, encrypted, and verified regularly—not just IT data.
05
Ignoring Insider Threat Vectors
Disgruntled employees, contractors with broad access, and unknowing insiders who click phishing links account for a significant share of industrial security incidents. Least-privilege access and behavioral monitoring are essential countermeasures.
06
No Separate Incident Response Plan for OT
A corporate IT incident response plan that does not address process isolation, safety system verification, and manual fallback procedures will fail when applied to a steel plant cyber incident—often making the situation significantly worse.
Build a Maintenance Operation That Is Secure by Design.
Oxmaint delivers role-based access, encrypted data flows, complete audit trails, and OT-compatible integration architectures that meet the security demands of connected steel plant environments—without disrupting the maintenance workflows your teams depend on every shift.
Frequently Asked Questions
What is OT cybersecurity and why does it matter for steel plants specifically?
OT cybersecurity refers to the protection of operational technology systems—PLCs, SCADA, DCS, HMIs, and industrial sensors—that directly control physical production processes. For steel plants, these systems manage blast furnace temperatures, rolling mill speeds, ladle handling, and continuous casting parameters. A cyberattack that manipulates these controls can cause physical equipment damage, personnel safety hazards, and production losses that far exceed the cost of any data breach in a corporate IT environment.
How should a CMMS be integrated into a steel plant OT network securely?
A CMMS should connect to OT data sources through a demilitarized zone (DMZ) using read-only, encrypted API connections rather than direct database access. All user accounts must use individual credentials with multi-factor authentication, and role-based permissions should limit each user to the minimum data required for their function. Integration architecture should be reviewed by both IT security and OT engineering teams before deployment, and all vendor connections should use time-limited, monitored sessions rather than permanent remote access tunnels.
Can legacy steel plant control systems be secured without replacement?
Yes, through compensating controls that protect legacy systems without requiring modification of the systems themselves. Network segmentation limits what can communicate with legacy PLCs and HMIs. Application whitelisting on engineering workstations prevents unauthorized software execution. Unidirectional data gateways allow monitoring data to flow out of the OT zone without allowing inbound attack traffic. These approaches can significantly reduce risk for systems that cannot be patched or updated on a standard IT security cadence.
What compliance standards apply to OT cybersecurity in steel manufacturing?
The primary international standard for industrial cybersecurity is IEC 62443, which defines security levels, zone architectures, and control requirements for industrial automation and control systems. NIST SP 800-82 provides guidance specifically for industrial control system security in North American contexts. Steel plants operating within critical infrastructure designations in certain jurisdictions may also fall under sector-specific regulations. Compliance with these frameworks typically requires asset inventory, access control, monitoring, and incident response capabilities that extend to CMMS and maintenance management systems.
How long does it take to implement OT cybersecurity improvements in a steel plant?
Quick wins—network segmentation review, credential audits, MFA enablement on maintenance systems, and vendor access cleanup—can typically be completed within sixty to ninety days without disrupting production. A comprehensive OT security program covering full asset inventory, passive monitoring deployment, incident response planning, and staff training usually matures over twelve to eighteen months. Starting with the highest-risk areas, particularly IT/OT integration points and remote access management, delivers the greatest early risk reduction per effort invested.