Facility managers and system administrators know that data integrity doesn't fail overnight—it degrades through decentralized spreadsheets, undocumented maintenance actions, and a lack of cryptographic verification. A comprehensive blockchain-backed ledger is your first line of defense against tampered logs, compliance violations, and missing asset histories. Studies show that organizations using distributed ledgers for maintenance experience a 40% reduction in audit times and achieve a 100% verifiable chain of custody for critical infrastructure. This guide walks you through everything you need to establish a bulletproof, tamper-evident asset tracking architecture.
Why Immutable Asset Data is Non-Negotiable
Poor data management accounts for a significant portion of compliance and operational costs. What starts as a minor undocumented repair or a misplaced spreadsheet can quickly escalate into a massive regulatory fine or a catastrophic equipment failure due to untracked lifecycle degradation. Understanding how cryptographic hashing and distributed nodes secure your asset data helps you prioritize accountability across your organization. You can start securing your asset data to begin tracking these critical maintenance logs today.
Cryptographic Tampering
A falsified safety check ignored becomes a massive liability when unverified components fail in production.
Regulatory Compliance Risks
Failed audits due to missing or altered maintenance records mean severe fines and operational halts.
Vendor SLA Disputes
Without a shared, immutable ledger, tracking third-party maintenance response times becomes a guessing game.
Lifecycle Blind Spots
Losing historical asset data and component lineage drastically reduces system reliability and resale value.
The Blockchain Implementation Checklist
This checklist is organized by implementation phase—start with creating digital identities for your assets, then work through smart contract automation and audit verification. For best results, integrate these cryptographic protocols into your existing CMMS workflow so no data point can be altered post-entry. Most successful tech-forward facilities create a secure account to digitize these ledgers instantly.
Phase 1: Digital Identity & IoT Integration
Phase 2: Smart Contract Automation
Phase 3: Audit & Traceability Verification
Understanding Data Integrity Levels
Not all data anomalies require the same response. Knowing when to monitor network sync issues versus when to lock down a system for a potential breach can mean the difference between a minor glitch and a compromised infrastructure. To ensure your data is always verified, you can deploy our blockchain-ready app.
Ledger Verification Response Guide
Secure Maintenance Data From Any Device
Stop relying on editable spreadsheets that fail audits. Our platform lets your team complete inspections with military-grade encryption and automated blockchain logging.
The Real Cost of Poor Data Traceability
Frequently Asked Questions
How does blockchain prevent maintenance data tampering?
Every time a maintenance log is created, it is encrypted into a block and linked to the previous one. To alter a past record, a malicious actor would have to rewrite the entire chain across multiple decentralized nodes, making undetected tampering mathematically impossible.
Do I need to understand cryptocurrency to use this?
Not at all. The underlying distributed ledger technology operates silently in the background of your CMMS. Your technicians simply use an app to close work orders, while the system handles the complex cryptographic hashing and data distribution.
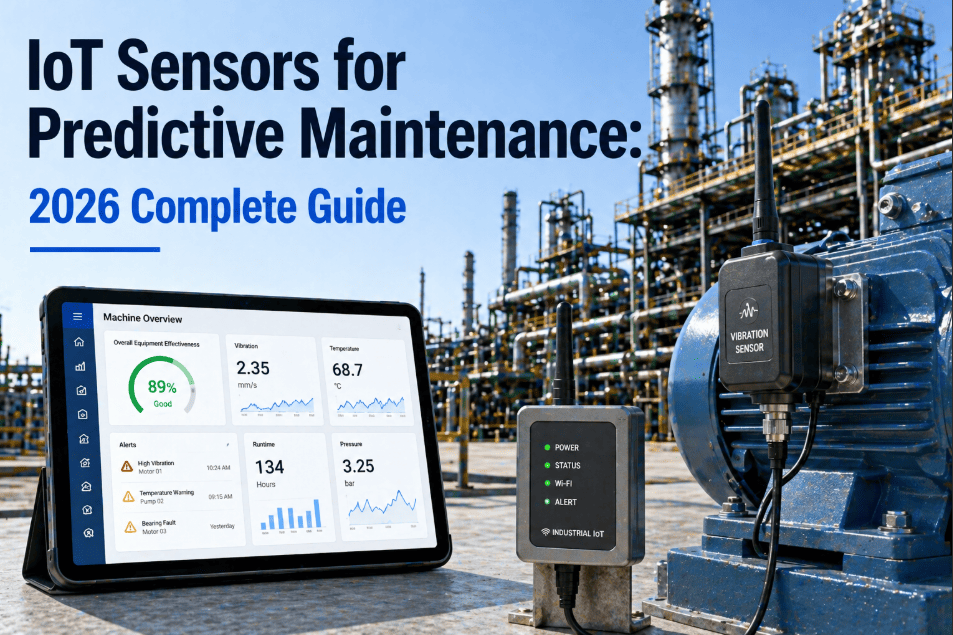
Can blockchain integrate with our existing IoT sensors and SCADA systems?
Yes. Modern blockchain maintenance platforms feature robust APIs that seamlessly ingest telemetry data from your existing IoT devices, SCADA systems, and PLCs, instantly converting real-time sensor readings into immutable ledger entries.
What happens if a technician makes a legitimate mistake in a logged work order?
Because blockchain is append-only, you cannot delete or overwrite the erroneous entry. Instead, the technician submits a new, corrected entry which is appended to the ledger. This maintains a 100% transparent audit trail showing the original mistake and the subsequent correction.
Will blockchain make our maintenance software slower?
No. Enterprise-grade distributed ledgers are specifically optimized for high-throughput industrial applications. The cryptographic hashing occurs in milliseconds, ensuring your frontline workers experience no latency when submitting work orders or scanning assets.
How does blockchain help with vendor and contractor management?
By using smart contracts, you can automate Service Level Agreements (SLAs). When a contractor completes a repair and logs it on the blockchain, the smart contract automatically verifies the timestamp and performance metrics, executing payments or flagging penalties without manual intervention.
Transform Your Asset Traceability Today
Join thousands of secure facilities utilizing decentralized ledgers to eliminate compliance risks and guarantee data integrity.