Every connected HVAC controller, BMS gateway, and IoT sensor in a commercial building is an endpoint on an operational technology (OT) network — and OT networks are now the fastest-growing target for ransomware and infrastructure attacks. The 2021 Oldsmar, Florida water treatment breach entered through a remote access tool. The 2013 Target data breach traced back to an HVAC vendor's network credentials. Connected building systems are no longer isolated infrastructure — they are attack surfaces that require the same structured maintenance discipline applied to physical equipment. OxMaint's Compliance Tracking platform embeds cybersecurity-aware workflows into HVAC maintenance — tracking firmware versions, access credentials, patch status, and vendor permissions alongside standard PM schedules.
The Five HVAC Cybersecurity Vulnerabilities Maintenance Teams Own
These are not IT problems — they are maintenance problems that require structured tracking in a CMMS, not a security information system.
Cybersecurity-Aware HVAC Maintenance Workflow
Integrating cybersecurity tasks into existing PM workflows requires no new team — it requires adding five fields to existing asset records and five tasks to existing PM checklists.
Track BMS Security Compliance Alongside Physical Maintenance
OxMaint's CMMS embeds firmware, credential, and access tracking directly into HVAC asset records and PM work orders — so cybersecurity compliance is maintained by the same team that maintains the equipment. Book a demo to see how it works.
Applicable Cybersecurity Standards for BMS and HVAC Systems
| Standard / Framework | Applies To | Key HVAC Requirement | Maintenance Team Role |
|---|---|---|---|
| NIST SP 800-82 | OT and ICS systems including BMS | Asset inventory, access control, patch management | Primary — asset records and patch tracking |
| IEC 62443 | Industrial control systems, BAS | Security zones, conduit management, update policies | Primary — zone documentation, firmware updates |
| ASHRAE Guideline 36 | HVAC controls and sequences | Control system documentation and change management | Primary — change logging in CMMS |
| CISA KEV Catalog | All networked building systems | Known exploited vulnerabilities requiring remediation | Support — firmware check against KEV advisory |
| SOC 2 / ISO 27001 | Buildings with tenant data obligations | Physical and environmental controls for building systems | Support — access log documentation for audits |
Expert Review
The misconception that stops most facility teams from acting on BMS cybersecurity is the belief that this is IT's responsibility. In practice, the physical maintenance team is the only group with regular, documented access to HVAC control hardware — and that makes them the only group positioned to enforce firmware patch schedules, credential rotation, and vendor access controls at the device level. A CMMS that tracks firmware version alongside filter replacement date is not overreaching into IT territory — it is completing the asset record that the IT team cannot complete because they do not have physical access to the plant room. The facilities that will face the most regulatory and insurance pressure over the next five years are the ones with networked building systems and no documented maintenance history for the cybersecurity-relevant attributes of those systems. The ones that will be protected are the ones whose CMMS work orders include a credential check alongside the refrigerant pressure check.
Make Cybersecurity Part of Every HVAC Work Order
OxMaint adds firmware, access, and credential tracking to HVAC asset records without adding a separate security system. Your maintenance team maintains the equipment — and the compliance record — in one place.
Frequently Asked Questions
Are HVAC and BMS systems really targets for cyberattacks?
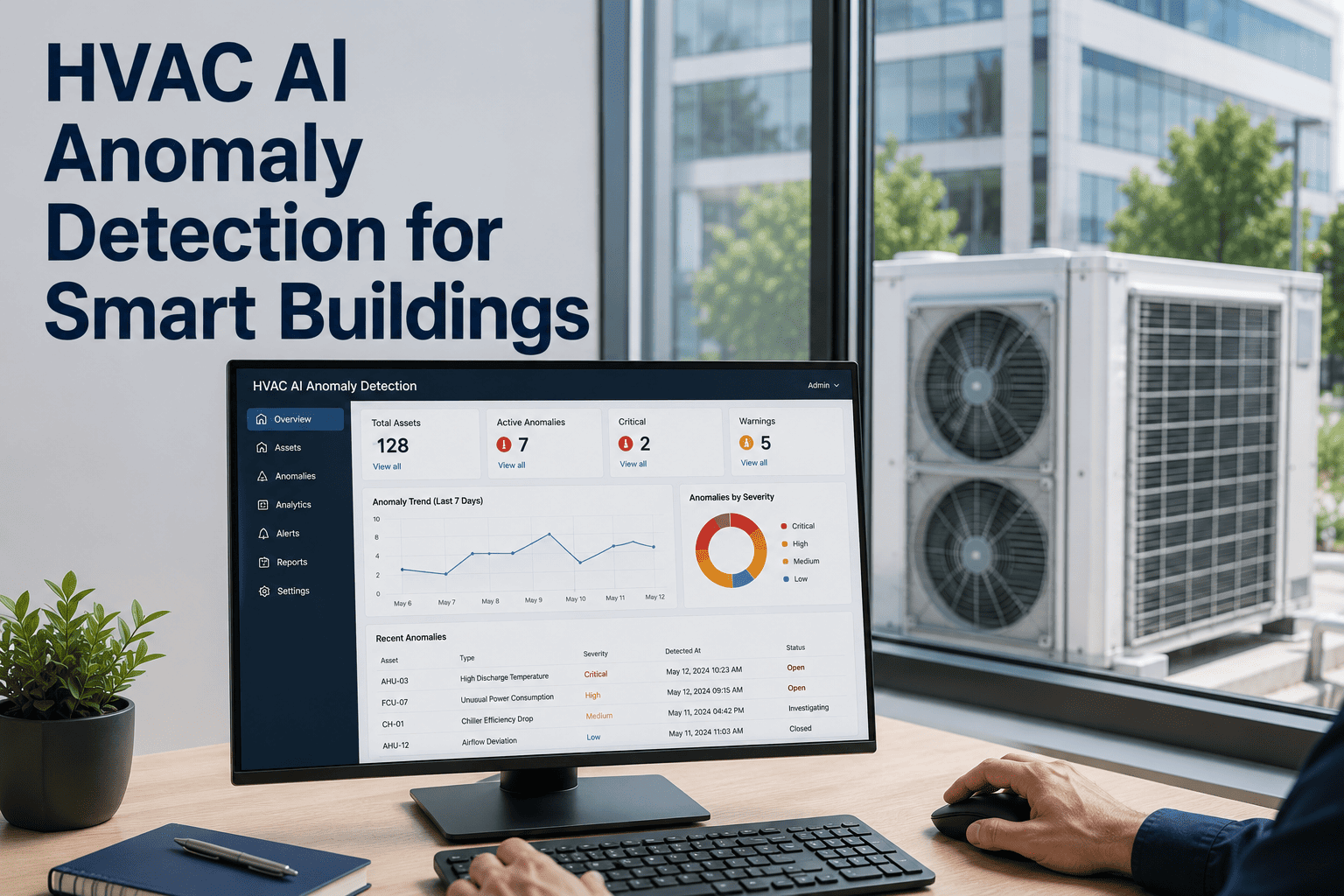
Yes — and the attack frequency is increasing. The CISA 2023 advisory on building automation systems documented 14 known exploited vulnerabilities in common BMS controller firmware actively used in ransomware campaigns. HVAC systems are targeted because they provide a networked entry point that is often less secured than IT endpoints, and because disrupting building climate control creates immediate operational pressure on facility operators. IBM's X-Force 2024 report identified building management systems as the third most commonly compromised OT environment, after energy utilities and manufacturing. OxMaint's compliance tracking maintains firmware and access records for every connected HVAC asset.
What is the maintenance team's responsibility in BMS cybersecurity?
The maintenance team is responsible for the physical and firmware-level security attributes of HVAC control assets — the components that IT security teams cannot access or audit without coordination. This includes maintaining an accurate asset inventory of all networked HVAC devices, tracking firmware versions and update history, managing vendor remote access credentials through a documented workflow, and logging all configuration changes in the CMMS work order record. These tasks require no cybersecurity expertise — they require the same documentation discipline already applied to physical PM tasks, with five additional fields per asset record. Book a demo to see how OxMaint structures these fields within standard asset records.
How often should HVAC firmware and BMS credentials be reviewed?
NIST SP 800-82 recommends annual firmware review for all OT assets, with patch application within 90 days of a vendor security release for any vulnerability rated CVSS 7.0 or above. Credential rotation should occur annually for standard access accounts and immediately following any service engagement where vendor credentials were provisioned. Remote access accounts should be audited quarterly — any account unused for 90 days should be deactivated pending re-authorization. OxMaint schedules these reviews as recurring PM tasks on the asset-specific maintenance calendar and tracks completion status in the compliance dashboard.
Does OxMaint integrate with cybersecurity or IT security management platforms?
OxMaint's CMMS generates structured asset records that include firmware version, network segment, credential history, and vendor access logs — data that can be exported to IT security information and event management (SIEM) platforms via API for correlation with network-level security monitoring. OxMaint does not replace security scanning tools but provides the physical asset record layer that contextualizes network security findings. For example, when a network scanner identifies an outdated BMS firmware version, the OxMaint asset record confirms which technician last serviced the device, whether a firmware update was included in the last PM scope, and which vendor has current remote access credentials.